OpenWebUI
Open WebUI: Dev Container + Terraform Azure Deployment Baseline
Portfolio Snapshot
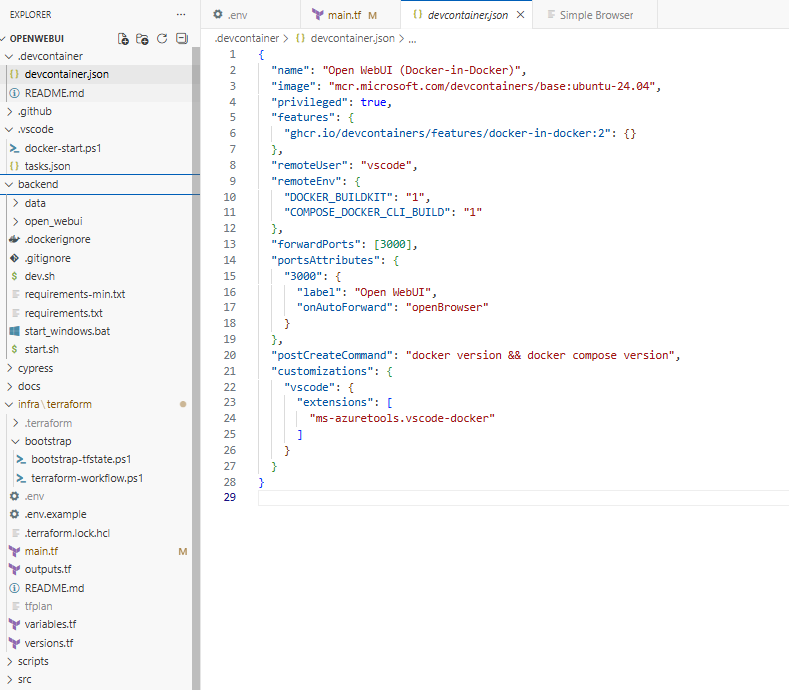
This project focuses on developer experience and cloud repeatability for Open WebUI. The local baseline uses a Dev Container configured for Docker-in-Docker so the app can be built and run with Docker Compose in a consistent environment. The cloud baseline uses Terraform to provision Azure Container Apps infrastructure (logging + environment + storage) and deploy a pinned Open WebUI container image with external ingress and platform-managed secrets. The result is a clean foundation for future iterations such as Entra ID authentication, stronger persistence (managed database), and additional platform tooling.
What it proves
- Ability to design a repeatable “local-to-cloud” workflow with minimal setup friction (Dev Container + Compose).
- Practical Infrastructure-as-Code skills: parameterized Terraform, AzureRM backend remote state, and reproducible deployments.
- Production-minded platform configuration: centralized logging (Log Analytics), secret injection via Container App secrets, and explicit ingress configuration.
- Good engineering judgment around persistence: demonstrates Azure Files mounts while avoiding known SQLite-on-SMB file locking reliability issues in the baseline.
Key components
- Dev Container (Docker-in-Docker) for consistent development
- Runs Docker + Docker Compose inside the container; avoids host machine drift.
- Port forwarding set up for the UI (3000) with an “open browser” experience.
-
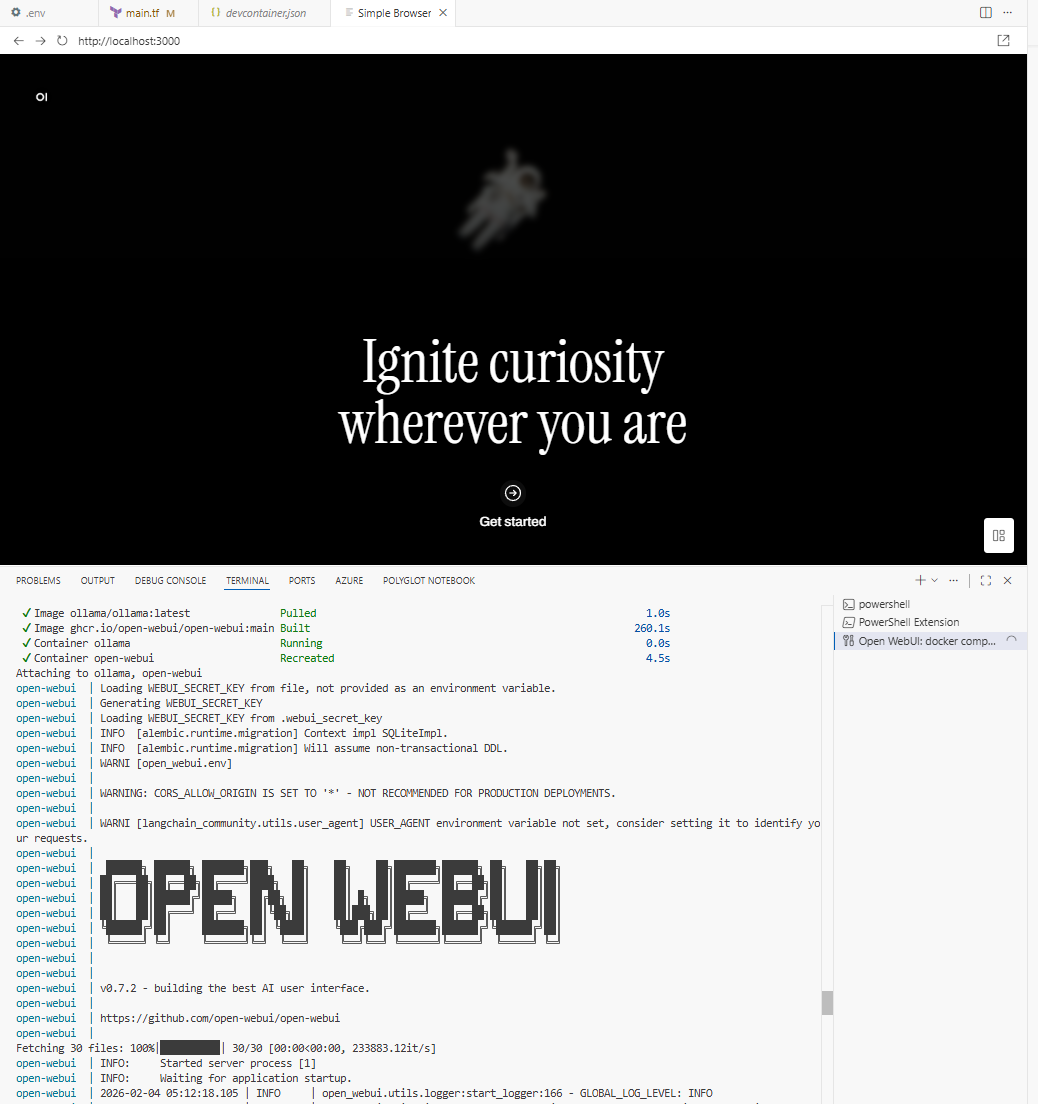
Local Docker Compose baseline (validation path)
- Open WebUI service plus an Ollama service for local integration and smoke testing.
- Named volume mount to persist local Open WebUI artifacts at
/app/backend/data.
-
Terraform Azure Container Apps deployment
- Resource group + Log Analytics workspace.
- Container Apps environment wired to Log Analytics.
- Open WebUI Container App with external ingress (target port 8080) and single-revision mode.
- Pinned Open WebUI image tag to keep deployments deterministic.
-
Storage + secrets
- Azure Storage Account + Azure Files share provisioned and mounted into the container at
/app/backend/data. WEBUI_SECRET_KEYstored as a Container App secret and injected as an environment variable.- Environment-driven configuration via a gitignored
.envfile usingTF_VAR_*.
- Azure Storage Account + Azure Files share provisioned and mounted into the container at
-
Operator automation
- PowerShell workflow script to standardize: bootstrap remote state → init → validate → plan → apply → destroy.
- VS Code tasks for end-to-end deploy flows and convenience operations.
Operational notes
- Remote Terraform state is intentionally configured at init-time (AzureRM backend values are supplied via environment), keeping state configuration out of Terraform source.
- Azure Files is used to persist artifacts/uploads/cache; SQLite is intentionally placed on local ephemeral storage to avoid SMB locking issues in the baseline.
- The infrastructure footprint is intentionally minimal (single replica, straightforward ingress) to optimize for clarity, repeatability, and future extension (Entra ID, managed DB, hardening).
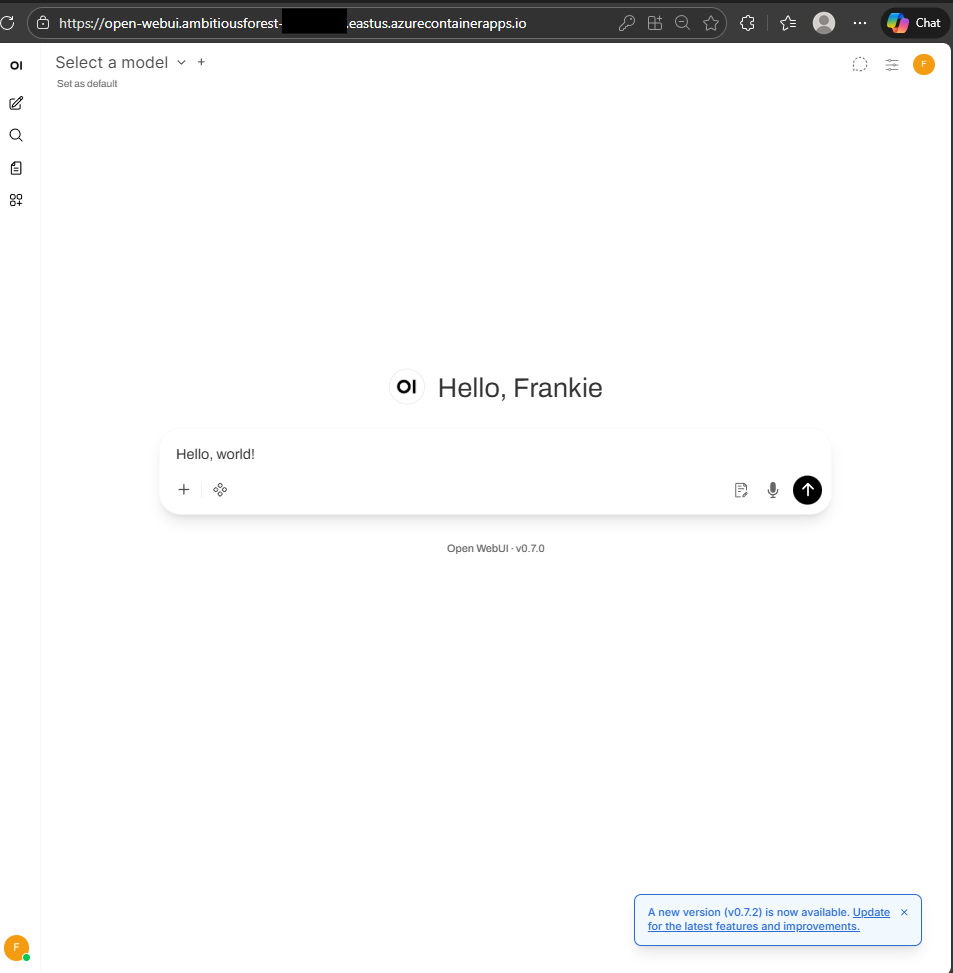
Verification
Visual evidence of project